💬 Course 6: Encrypted Messages PREMIUM
Learning Objectives
- Understand the complete history of encrypted communication from ancient ciphers to modern cryptography
- Master the difference between symmetric and asymmetric encryption and when to use each
- Explain how AES-256 works and why it is considered unbreakable
- Understand how end-to-end encryption works and why it matters for privacy
- Learn about the Signal Protocol and how it achieves forward secrecy
- Understand PGP, the Web of Trust model, and their role in cryptocurrency culture
- Understand on-chain vs off-chain messaging architectures in blockchain systems
- Learn how Kenostod's transaction messages are cryptographically signed and verified
- Analyze metadata protection challenges and traffic analysis attacks
- Explore zero-knowledge proofs and their application to private messaging
- Compare privacy coins and their messaging features (Monero, Zcash, Secret Network)
- Apply practical encryption workflows to real-world business and compliance scenarios
This course is designed for thorough learning. Plan for ~2 hours of reading, exercises, and practice. Take breaks between sections. True understanding takes time, and the 250 KENO reward reflects that commitment.
Introduction: Why Encrypted Messages Matter
Traditional blockchain transactions are just numbers — an amount transferred from address A to address B. But in the real world, context matters enormously. When you pay a contractor, you need to reference an invoice. When you send money to family overseas, compliance regulations may require a purpose code. When two businesses settle accounts, both parties need a verifiable record of what the payment was for.
Kenostod solves this by allowing you to attach cryptographically-signed, optionally encrypted messages to any transaction. These messages become part of the immutable blockchain record — they cannot be altered, denied, or forged after sending.
Think of it this way: a traditional blockchain transaction is like handing someone an envelope of cash. A Kenostod transaction message is like handing them cash with a notarized letter — everyone can see the letter was sent and who signed it, but only the recipient can read the contents if it's encrypted.
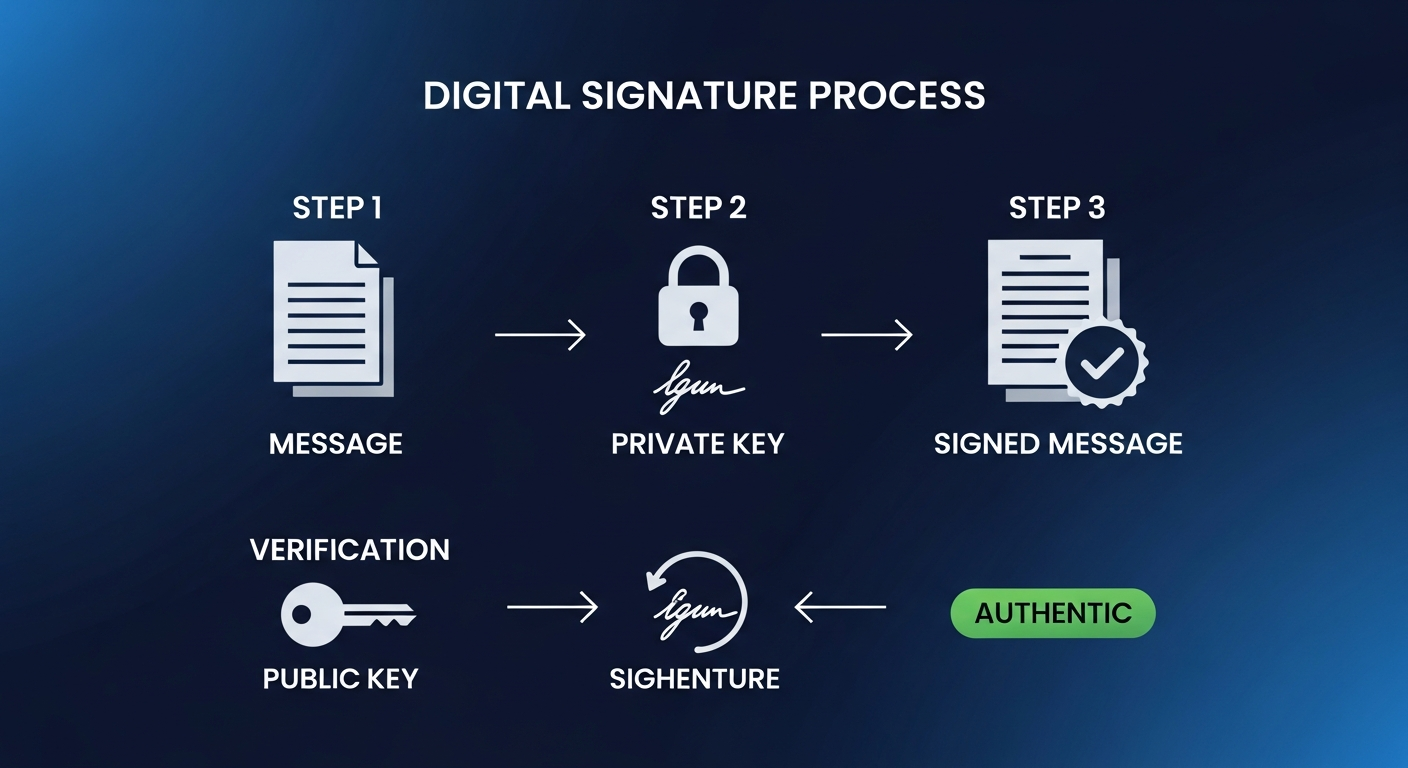
Figure: Messages embedded in transactions with cryptographic verification
This capability transforms a simple payment network into a verifiable communication layer. Every message is timestamped, attributed, and permanent. This has profound implications for business, law, compliance, and personal privacy that we'll explore throughout this course.
The Communication Gap in Blockchain
Most blockchain networks were designed purely as financial ledgers. Bitcoin, for example, has a tiny OP_RETURN field that allows storing up to 80 bytes of arbitrary data — barely enough for a short sentence. Ethereum allows input data in transactions, but this data is stored as raw hex and isn't designed for human-readable communication. Neither network was built with structured, encrypted messaging as a first-class feature.
This creates a fundamental disconnect: businesses adopt blockchain for transparent, verifiable financial transactions, but then must use separate, unverifiable channels (email, Slack, phone calls) to communicate about those transactions. The payment says "$5,000 to 0xABC..." but the context — what was it for? Was the work satisfactory? Were the terms met? — lives outside the chain, vulnerable to disputes, forgery, and loss.
💡 Tamper-Proof Communication
Unlike email or text messages, transaction messages are cryptographically signed and permanently recorded on the blockchain. The message becomes part of the transaction itself — it cannot be altered, deleted, or denied after sending. This is called non-repudiation: the sender cannot later claim they didn't write or send the message, because the cryptographic signature mathematically proves they did.
Three Modes of Kenostod Messages
Kenostod supports three distinct messaging modes, each serving different use cases:
| Mode | Visibility | Use Case | Example |
|---|---|---|---|
| Plaintext | Anyone can read | Public records, donations, tips | "Donation to Kenostod Dev Fund - Q4 2024" |
| Encrypted | Only recipient | Invoices, salary, private notes | "Invoice #2024-001: Web development - $500" |
| Hashed Reference | Verifiable but private | Legal documents, contracts | SHA-256 hash of a PDF contract stored off-chain |
The History of Encrypted Communication
The desire to communicate secretly is as old as civilization itself. Understanding the evolution of cryptography helps us appreciate why modern blockchain-based messaging is such a breakthrough — and why the techniques used in Kenostod represent thousands of years of human ingenuity.
Ancient Cryptography (2000 BCE – 1800s)
The earliest known use of cryptography dates back to ancient Egypt around 1900 BCE, where scribes used non-standard hieroglyphics in inscriptions. However, the first well-documented cipher system was the Spartan Scytale (700 BCE) — a leather strip wrapped around a rod of specific diameter. The message was readable only when wrapped around a rod of the same size.
The most famous ancient cipher is the Caesar Cipher (100 BCE), used by Julius Caesar to communicate with his generals. Each letter was shifted by a fixed number: with a shift of 3, A becomes D, B becomes E, and so on. While trivially easy to break today, it was effective 2,000 years ago when most people were illiterate.
The Vigenère Cipher (1553) improved on Caesar by using a keyword to vary the shift for each letter, making frequency analysis much harder. It was considered "the indecipherable cipher" for three centuries until Charles Babbage and Friedrich Kasiski independently broke it in the mid-1800s.
The Mechanical Age (1900s – 1940s)
World War II brought cryptography into the mechanical age. The German Enigma machine used rotating electromechanical rotors to create enormously complex substitution ciphers. The machine had approximately 158,962,555,217,826,360,000 possible settings for each message.
Breaking Enigma at Bletchley Park, led by Alan Turing and his team, is estimated to have shortened World War II by two years and saved millions of lives. Turing's work also laid the theoretical foundations for modern computing — the same mathematics that eventually enabled blockchain technology.
The direct line from Turing's codebreaking to modern cryptography is remarkable. Turing's concept of a "universal computing machine" led to electronic computers, which led to computational cryptography, which led to public-key cryptography in the 1970s, which is the exact foundation of blockchain wallets and transaction signing today. When you sign a transaction in Kenostod, you're using mathematics that traces directly back to Bletchley Park.
A Timeline of Cryptographic Milestones
1900 BCE — Egyptian Hieroglyphic Substitution
Scribes in Khnumhotep II's tomb used non-standard symbols to obscure inscriptions, the earliest known cryptographic technique.
700 BCE — Spartan Scytale
First transposition cipher using a physical device (wooden rod) to scramble messages on leather strips.
100 BCE — Caesar Cipher
Julius Caesar shifts alphabet letters by a fixed amount. Simple but effective for its era.
1553 — Vigenère Cipher
Polyalphabetic substitution using a keyword. Called "le chiffre indéchiffrable" for 300 years.
1918 — Enigma Machine Patented
Arthur Scherbius patents the electromechanical rotor cipher machine later used by Nazi Germany.
1943 — Colossus Computer
Built at Bletchley Park to break the Lorenz cipher. One of the world's first programmable electronic computers.
1976 — Diffie-Hellman Key Exchange
The concept of public-key cryptography is born. Two parties can establish a shared secret over a public channel.
1977 — RSA & DES
RSA provides the first practical public-key encryption. DES becomes the government standard for symmetric encryption.
1991 — PGP Released
Phil Zimmermann publishes Pretty Good Privacy, bringing strong encryption to ordinary citizens.
2001 — AES Adopted
Advanced Encryption Standard replaces DES as the global standard. AES-256 remains unbroken to this day.
2009 — Bitcoin Launches
Satoshi Nakamoto combines cryptographic signatures, hashing, and peer-to-peer networking into the first cryptocurrency.
2013 — Signal Protocol
Moxie Marlinspike develops the Double Ratchet Algorithm, enabling forward secrecy in messaging.
Present — Kenostod Encrypted Messages
Combining blockchain immutability with ECIES encryption to create verifiable, private transaction communication.
The Digital Revolution (1970s – 2000s)
Three pivotal developments transformed cryptography forever:
1. DES — Data Encryption Standard (1977)
The U.S. government standardized DES as the first publicly available encryption algorithm. Using a 56-bit key, it became the backbone of electronic financial transactions. Though eventually broken by brute force, DES proved that standardized, publicly scrutinized algorithms are stronger than secret, proprietary ones — a principle called Kerckhoffs's principle.
2. Diffie-Hellman Key Exchange (1976)
Whitfield Diffie and Martin Hellman published the revolutionary concept of public-key cryptography. For the first time, two parties could establish a shared secret over a public channel without ever meeting. This solved the fundamental problem of key distribution that had plagued cryptography for millennia.
Imagine this analogy: Alice and Bob each have a color of paint (their private keys). They agree on a shared base color publicly (yellow). Each mixes their private color with yellow and sends the result. Then each mixes their private color with the other's result. Both end up with the same final color, but an eavesdropper who only saw the mixed colors cannot determine the final result.
3. RSA (1977) and Elliptic Curve Cryptography (1985)
RSA, developed by Rivest, Shamir, and Adleman, was the first practical public-key encryption system. Based on the difficulty of factoring large prime numbers, RSA enabled both encryption and digital signatures. Later, Elliptic Curve Cryptography (ECC) achieved the same security with much smaller keys — a 256-bit ECC key provides equivalent security to a 3,072-bit RSA key. ECC is what Bitcoin, Ethereum, and Kenostod use today.
The Cypherpunk Movement (1992 – Present)
The cypherpunk movement believed that cryptography was essential for privacy in the digital age. Members included many who would later influence cryptocurrency: Adam Back (inventor of Hashcash, a precursor to Bitcoin's proof-of-work), Wei Dai (inventor of b-money), and Hal Finney (received the first Bitcoin transaction from Satoshi Nakamoto). The cypherpunk mailing list directly shaped the ideas that became Bitcoin and, by extension, all blockchain technology including Kenostod.
💡 The Cypherpunk Vision Realized
Eric Hughes wrote in the 1993 A Cypherpunk's Manifesto: "Privacy is necessary for an open society in the electronic age... We must defend our own privacy if we expect to have any." Kenostod's encrypted transaction messages are a direct realization of this vision — private, verifiable communication built on cryptographic foundations.
Symmetric Encryption Deep Dive
Symmetric encryption uses the same key for both encrypting and decrypting data. Think of it like a physical lockbox — the same key opens and closes it. Both the sender and receiver must possess the identical key.
How Symmetric Encryption Works
The process is straightforward:
- Key Generation: A random secret key is generated (e.g., 256 random bits for AES-256). The quality of randomness is critical — a predictable key generator can compromise even the strongest algorithm.
- Encryption: The plaintext message is combined with the key using a mathematical algorithm to produce ciphertext. Modern ciphers like AES use multiple rounds of substitution and permutation.
- Transmission: The ciphertext is sent over the (potentially insecure) channel. Even if intercepted, the ciphertext is computationally indistinguishable from random data.
- Decryption: The recipient uses the same key to reverse the process and recover the plaintext. The algorithm's inverse operations are applied in reverse order.
AES-256 — The Gold Standard
Advanced Encryption Standard (AES) is the most widely used symmetric cipher today. Adopted by the U.S. government in 2001 after a five-year international competition involving 15 candidate algorithms from around the world, AES (originally called Rijndael, after its Belgian creators Joan Daemen and Vincent Rijmen) is considered unbreakable by any known technology.
AES operates on 128-bit blocks of data. In AES-256 mode, it uses a 256-bit key and performs 14 rounds of transformation. Each round consists of four operations:
- SubBytes: Each byte is replaced using a substitution table (S-box), providing non-linearity
- ShiftRows: Rows of the state matrix are cyclically shifted, providing diffusion
- MixColumns: Columns are mixed using matrix multiplication in a finite field
- AddRoundKey: The round key (derived from the original key) is XORed with the state
To brute-force AES-256, you would need to try 2256 possible keys. That's approximately 1.16 × 1077 combinations. If every atom in the observable universe (approximately 1080) were a computer trying one billion keys per second, it would still take longer than the age of the universe to try all possibilities.
Block Cipher Modes of Operation
AES encrypts data in fixed 128-bit blocks. When messages are longer than 128 bits (16 bytes), a mode of operation determines how blocks are chained together:
| Mode | Description | Security | Use Case |
|---|---|---|---|
| ECB | Each block encrypted independently | Weak — identical blocks produce identical ciphertext | Never use for messages |
| CBC | Each block XORed with previous ciphertext | Good, but vulnerable to padding oracle attacks | Legacy systems, TLS 1.2 |
| CTR | Encrypts a counter value, XORed with plaintext | Good, parallelizable | High-speed encryption |
| GCM | CTR mode + authentication tag | Excellent — authenticated encryption | TLS 1.3, Kenostod messages |
Kenostod uses AES-256-GCM (Galois/Counter Mode) for message encryption. GCM provides both confidentiality (no one can read the message) and authenticity (no one can tamper with the ciphertext without detection). The authentication tag ensures that if even a single bit of the ciphertext is modified, decryption will fail — protecting against both eavesdropping and tampering.
The Key Distribution Problem
Symmetric encryption has one fundamental weakness: how do you securely share the key? If you could securely send the key to the recipient, you could have just securely sent the message instead. This is called the key distribution problem, and it plagued cryptography for centuries until public-key cryptography solved it.
In practice, modern systems use a hybrid approach: asymmetric encryption (slow but no key sharing needed) is used to securely exchange a symmetric key, which is then used for the actual data encryption (fast and efficient). This is exactly how HTTPS, Signal, WhatsApp, and Kenostod's encrypted messages work.
| Property | Symmetric | Asymmetric |
|---|---|---|
| Key count | One shared key | Key pair (public + private) |
| Speed | Very fast (1000x+) | Slow |
| Key distribution | Must be shared secretly | Public key shared openly |
| Key size (equiv. security) | 128-256 bits | 2048-4096 bits (RSA) / 256 bits (ECC) |
| Best for | Bulk data encryption | Key exchange, signatures |
| Example algorithms | AES, ChaCha20, Twofish | RSA, ECDSA, Ed25519, X25519 |
| Quantum resistance | AES-256 remains secure (Grover's reduces to 128-bit) | RSA/ECC broken by Shor's algorithm |
Quantum computers running Shor's algorithm could break RSA and ECC, but AES-256 remains quantum-resistant (Grover's algorithm only halves the effective key length, reducing it to 128-bit equivalent security — still unbreakable). This is why the cryptography community is actively developing post-quantum cryptographic algorithms. Kenostod's roadmap includes migration to quantum-resistant signature schemes when standardized.
Asymmetric Encryption Deep Dive
Asymmetric encryption (also called public-key cryptography) uses a mathematically linked pair of keys: a public key that anyone can know, and a private key that only the owner possesses. Data encrypted with the public key can only be decrypted with the corresponding private key, and vice versa.
The Mailbox Analogy
Think of a mailbox with a slot (the public key) and a key to open it (the private key). Anyone can drop a letter into the slot, but only the person with the key can retrieve the letters. Even the person who dropped the letter in cannot get it back. This is exactly how asymmetric encryption works: anyone can encrypt a message with your public key, but only you can decrypt it with your private key.
Elliptic Curve Cryptography in Kenostod
Kenostod uses secp256k1, the same elliptic curve used by Bitcoin and Ethereum. An elliptic curve is defined by the equation y2 = x3 + ax + b. For secp256k1, the specific equation is y2 = x3 + 7.
The security relies on the Elliptic Curve Discrete Logarithm Problem (ECDLP): given a point P on the curve and another point Q = kP (where k is the private key), it's computationally infeasible to determine k from P and Q. This is a one-way function — easy to compute in one direction, virtually impossible to reverse.
ECIES — Elliptic Curve Integrated Encryption Scheme
Kenostod uses ECIES for message encryption, which combines the best of both worlds. The full process is elegant in its design:
- Step 1: Generate a random ephemeral key pair (used once, then discarded)
- Step 2: Use ECDH (Elliptic Curve Diffie-Hellman) with the recipient's public key to derive a shared secret
- Step 3: Use a Key Derivation Function (KDF) to derive an AES key and MAC key from the shared secret
- Step 4: Encrypt the message with AES-256-GCM (symmetric, fast, authenticated)
- Step 5: Include the ephemeral public key with the ciphertext so the recipient can reconstruct the shared secret
This hybrid approach gives us the convenience of asymmetric encryption (no need to pre-share keys) with the speed of symmetric encryption (AES for bulk data). Each message gets a unique symmetric key, so compromising one message's key doesn't affect any other message.
RSA vs ECC: Why Kenostod Chose Elliptic Curves
| Property | RSA-3072 | ECC-256 (secp256k1) |
|---|---|---|
| Security level | 128-bit equivalent | 128-bit equivalent |
| Key size | 3072 bits (384 bytes) | 256 bits (32 bytes) |
| Signature size | 384 bytes | 64 bytes |
| Sign speed | Slower | Faster |
| Verify speed | Faster | Slightly slower |
| Blockchain suitability | Poor (large signatures waste block space) | Excellent (compact signatures) |
ECC's compact key and signature sizes make it ideal for blockchain systems where every byte stored on-chain costs money. A 64-byte ECDSA signature vs a 384-byte RSA signature means 6x less storage per transaction — a massive savings at scale.
Every Kenostod wallet already has a public-private key pair (that's what a wallet IS). This means every wallet is automatically capable of receiving encrypted messages — no additional setup required. Your wallet's public key doubles as your encryption key, and your private key doubles as your decryption key. The infrastructure for secure communication was built into the payment system from day one.
End-to-End Encryption Explained
End-to-end encryption (E2EE) means that only the communicating parties can read the messages. No intermediary — not the service provider, not the network operators, not even the developers — can access the plaintext content.
How E2EE Differs from Transport Encryption
Many services claim to use encryption but only encrypt data "in transit" (like HTTPS). This is called transport encryption — the data is encrypted between your device and the server, but the server itself can read everything. This is how most email services work: Google can read your Gmail, Microsoft can read your Outlook.
With E2EE, the message is encrypted on the sender's device and only decrypted on the recipient's device. The server (or blockchain) only ever sees ciphertext. Even if the server is compromised, the messages remain unreadable.
The Signal Protocol
The Signal Protocol, developed by Moxie Marlinspike and Open Whisper Systems, is widely considered the gold standard for encrypted messaging. Used by Signal, WhatsApp (2+ billion users), and Facebook Messenger, it provides three groundbreaking properties:
Forward Secrecy (via the Double Ratchet)
Even if a key is compromised, past messages remain secure. Signal achieves this through the Double Ratchet Algorithm, which continuously generates new encryption keys. Think of it like a ratchet wrench — it can only move forward, never backward. Each message uses a new key derived from the previous state, so compromising the current key reveals nothing about past keys.
Future Secrecy (Self-Healing)
Even if a key is compromised, future messages become secure again after a few exchanges. The Diffie-Hellman ratchet generates new key material with each exchange, so the attacker's advantage is temporary.
Deniability
Messages cannot be cryptographically proven to come from a specific person to a third party. This is a deliberate design choice — it means a leaked conversation cannot be mathematically verified as authentic, protecting sources and whistleblowers.
How Kenostod Messaging Compares to Signal
Kenostod's approach differs from Signal in important ways, each with trade-offs:
| Feature | Signal Protocol | Kenostod Messages |
|---|---|---|
| Permanence | Messages can be deleted | Messages are permanent (on-chain) |
| Non-repudiation | Deniable by design | Cryptographically signed (non-deniable) |
| Forward secrecy | Yes (Double Ratchet) | No (static wallet keys) |
| Metadata privacy | Minimal metadata (sealed sender) | Transaction metadata is public |
| Use case | Private conversation | Verifiable business communication |
| Legal standing | Weak (deniable by design) | Strong (signed, timestamped, immutable) |
| Key management | Automatic (app handles it) | Wallet-based (user controls keys) |
| Cost per message | Free (centralized infrastructure) | Transaction fee (block space) |
| Offline delivery | Yes (server queues) | Yes (stored on-chain permanently) |
💡 Different Tools for Different Jobs
Signal is designed for private conversation where deniability is a feature. Kenostod messages are designed for verifiable business communication where non-repudiation is the feature. You wouldn't use Signal for a legally binding contract acknowledgment, and you wouldn't use Kenostod messages for casual private chats. Understanding which tool fits which purpose is key to using them correctly.
PGP & the Web of Trust
PGP (Pretty Good Privacy) was created by Phil Zimmermann in 1991 and represents one of the most important chapters in the history of civilian cryptography. Its creation, the legal battles it sparked, and the trust model it introduced all directly influenced the cryptocurrency movement.
The Birth of PGP
In 1991, the U.S. government was considering Senate Bill 266, which would have required all electronic communications to include a "backdoor" for government access. Phil Zimmermann, a software engineer and political activist, decided to release PGP as freeware before the bill could pass, believing that strong encryption was a fundamental right.
The U.S. government responded by investigating Zimmermann for three years under the Arms Export Control Act, which classified strong encryption software as "munitions" — the same category as missiles and tanks. The investigation was eventually dropped in 1996, but the Crypto Wars it sparked established crucial legal precedents for the right to use strong encryption.
How PGP Works
PGP uses a hybrid encryption approach similar to what Kenostod employs:
The Web of Trust
PGP introduced the Web of Trust model for establishing identity without a central authority. Instead of a Certificate Authority (like in HTTPS), PGP users verify each other's identities and sign each other's public keys. If Alice trusts Bob, and Bob has signed Charlie's key, Alice can reasonably trust Charlie's key through Bob's endorsement.
This decentralized trust model is conceptually identical to how blockchain networks establish trust without a central authority. In fact, many early Bitcoin adopters were PGP users who understood the power of decentralized cryptographic systems. Satoshi Nakamoto's first Bitcoin announcement was posted to a cryptography mailing list where PGP signatures were standard practice.
PGP in Cryptocurrency Culture
PGP remains deeply embedded in cryptocurrency culture:
- Key Signing Parties: Cryptocurrency meetups often include PGP key signing sessions where participants verify each other's identities
- Canary Statements: Exchanges and services use PGP-signed "warrant canary" statements to indicate they haven't been served with secret government orders
- Developer Communication: Bitcoin Core developers sign their commits and communications with PGP keys, establishing a chain of trusted development
- Darknet Markets: PGP encryption was standard for buyer-seller communication on early cryptocurrency marketplaces
PGP's Limitations (and How Kenostod Improves)
Despite its technical soundness, PGP email encryption never achieved mass adoption. The reasons are instructive for understanding why Kenostod's approach is better:
| PGP Problem | Kenostod Solution |
|---|---|
| Complex key management (import, export, verify) | Wallet keys serve as encryption keys automatically |
| No forward secrecy (one key compromise = all messages) | Each message uses unique ephemeral keys (ECIES) |
| Metadata leaks (subject, sender, recipient, timestamps) | Only transaction metadata is public; message content encrypted |
| Key discovery problem (how to find someone's public key?) | Public key is derivable from wallet address |
| No built-in financial context | Messages are inherently tied to financial transactions |
While PGP itself may be declining in everyday use, its core innovations — hybrid encryption, the Web of Trust, and the principle that civilians deserve strong encryption — are the foundation of every modern encrypted system, including Kenostod. Understanding PGP helps you understand why blockchain-based encrypted messaging exists at all.
Blockchain Messaging: On-Chain vs Off-Chain
When we talk about "blockchain messaging," there are fundamentally two architectures, each with significant trade-offs:
On-Chain Messaging (Kenostod's Approach)
On-chain messaging stores the message data directly on the blockchain as part of a transaction. This is Kenostod's approach, and it provides unmatched guarantees:
- Permanence: Messages are immutable — stored forever on every node in the network
- Verifiability: Anyone can verify the message exists and who sent it by checking the blockchain
- Timestamping: The block timestamp provides a tamper-proof time record, accepted as evidence in many jurisdictions
- Censorship resistance: No single entity can delete or censor the message once confirmed
- Cost: Messages consume block space, so they incur transaction fees proportional to message size
- Size limits: Block size constraints limit message length (Kenostod allows up to 4KB per message)
- Privacy trade-off: Even encrypted messages reveal that communication occurred between two addresses
Off-Chain Messaging
Off-chain messaging stores messages separately from the blockchain, using it only for verification or key exchange:
- Scalability: No block space consumed, so no size limits and no additional fees
- Lower cost: No transaction fees for messages
- Privacy: Communication patterns not recorded on public chain
- Rich media: Can include images, files, and large documents
- Fragility: If the off-chain storage fails, messages are permanently lost
- Trust requirement: Must trust the off-chain storage provider to not tamper with or delete data
- No guaranteed delivery: The storage provider could censor specific messages
The Hybrid Model
Many projects use a hybrid approach: a hash of the message is stored on-chain (proving it existed at a certain time and hasn't been altered), while the full message is stored off-chain (IPFS, Arweave, or private servers). This provides verifiability without the cost of storing large messages on-chain.
Real-World Blockchain Messaging Protocols
Several blockchain projects have tackled messaging in different ways. Understanding the landscape helps you appreciate Kenostod's unique position:
| Protocol | Architecture | Key Feature | Limitation |
|---|---|---|---|
| XMTP | Off-chain (own network) | Wallet-to-wallet messaging, E2EE | Not tied to transactions |
| Push Protocol | Hybrid | Decentralized notifications | Focused on notifications, not conversation |
| Waku | Off-chain (libp2p) | Censorship-resistant, minimal metadata | No built-in financial context |
| Ethereum Input Data | On-chain | Arbitrary data in transactions | No encryption standard, raw hex |
| Kenostod Messages | On-chain | Integrated with payments, ECIES encryption | Size limited, transaction fee required |
Kenostod's approach is unique in tying messages directly to transactions. While protocols like XMTP provide general messaging, Kenostod messages have an inherent financial context — they're always associated with a specific payment, creating an unbreakable link between communication and economic activity. This makes them ideal for business applications where you need to prove not just that you communicated, but exactly what you communicated in relation to a specific financial transaction.
Digital Signatures & Message Signing
Every Kenostod transaction message is digitally signed with the sender's private key. This provides three critical guarantees:
- Authentication: The message was definitely sent by the owner of the wallet. No one else could have produced the signature without the private key. This is stronger than any physical signature — it's mathematically impossible to forge.
- Integrity: The message has not been altered since it was signed. Changing even a single character would invalidate the signature. Even adding a space or period produces a completely different hash.
- Non-repudiation: The sender cannot deny having sent the message. The mathematical proof is irrefutable and can be verified by anyone with access to the public key (which is everyone, since public keys are public).
How Message Signing Works
ECDSA vs EdDSA
Kenostod uses ECDSA (Elliptic Curve Digital Signature Algorithm) on secp256k1 for compatibility with the broader blockchain ecosystem. However, newer systems are adopting EdDSA (Edwards-curve Digital Signature Algorithm) on Curve25519, which offers several advantages:
| Property | ECDSA (secp256k1) | EdDSA (Ed25519) |
|---|---|---|
| Deterministic | No (requires random nonce) | Yes (deterministic nonce) |
| Nonce vulnerability | Reused nonce = key leak | No risk (deterministic) |
| Speed | Good | Faster |
| Ecosystem | Bitcoin, Ethereum, Kenostod | Solana, Cardano, newer chains |
| Batch verification | Limited | Excellent |
Legal Implications of Signed Messages
Cryptographically signed messages have increasingly recognized legal standing. In many jurisdictions, a digital signature carries the same weight as a handwritten signature under laws like:
- U.S. E-SIGN Act (2000): Electronic signatures are legally valid for commerce
- EU eIDAS Regulation (2014): Establishes three levels of electronic signatures, with "qualified electronic signatures" having the highest legal standing
- UNCITRAL Model Law: Provides international framework for electronic signatures
This means Kenostod transaction messages can potentially serve as:
- Proof of agreement to contract terms
- Acknowledgment of receipt of goods or services
- Timestamped evidence in disputes
- Audit trails for regulatory compliance
- Tax documentation with verifiable payment records
- Supply chain provenance verification
While cryptographic signatures are mathematically irrefutable, their legal standing depends on jurisdiction and the specific legal framework. The challenge is often proving the connection between a cryptographic key and a real-world identity. Always consult a legal professional for matters requiring formal contracts or compliance documentation.
Metadata Protection Challenges
Encrypting message content is only half the privacy battle. Metadata — information about the communication itself — can be just as revealing as the content. As former NSA General Counsel Stewart Baker said: "Metadata absolutely tells you everything about somebody's life. If you have enough metadata, you don't really need content."
What Metadata Reveals
Even with perfectly encrypted message content, blockchain transactions reveal:
- Sender address: Who initiated the communication
- Recipient address: Who received it
- Timestamp: When the communication occurred
- Transaction amount: The financial value attached
- Message size: How long the encrypted message is (reveals rough content length)
- Frequency: How often two addresses communicate
- Network analysis: Who communicates with whom, forming a social graph
Consider this scenario: An encrypted message is sent from a known corporate wallet to a regulator's wallet, followed by a large sell-off of the company's tokens. An observer can't read the message, but the metadata alone suggests insider knowledge of an upcoming regulatory action. The pattern of communication reveals intent, even without knowing the content.
Traffic Analysis Attacks
Traffic analysis is the study of communication patterns to extract intelligence without reading message contents. It has a long history in military intelligence and has become increasingly relevant in the blockchain era:
Timing Correlation
If Alice sends a transaction at 3:47:22 PM and a "anonymous" transaction appears on another network at 3:47:25 PM, the timing correlation suggests they're related. Sophisticated adversaries can correlate timing across chains, exchanges, and IP addresses.
Amount Correlation
Sending exactly 1,337.42 KENO is distinctive. Even after mixing or tumbling, if the same unusual amount appears elsewhere, it can be traced. This is why privacy-focused users often use round numbers or add random noise to amounts.
Graph Analysis
By mapping which addresses transact with which, analysts can build a social graph. Clustering algorithms can group addresses belonging to the same entity. Companies like Chainalysis, Elliptic, and CipherTrace have built billion-dollar businesses doing exactly this.
Metadata Protection Techniques
Various techniques exist to mitigate metadata leakage, each with trade-offs:
| Technique | What It Protects | Trade-off |
|---|---|---|
| Stealth Addresses | Recipient identity (one-time addresses) | More complex key management |
| Tor/I2P | IP address of sender | Slower transaction broadcasting |
| CoinJoin/Mixing | Transaction graph (who paid whom) | Higher fees, requires coordination |
| Confidential Transactions | Transaction amounts | Larger transaction sizes |
| Decoy Traffic | Communication patterns | Wasted bandwidth and fees |
| Delayed Broadcasting | Timing correlation | Slower message delivery |
Kenostod's Metadata Posture
Kenostod takes a pragmatic approach: transaction metadata (amounts, addresses, timestamps) is transparent, but message content is optionally encrypted. This is a deliberate design choice that prioritizes:
- Auditability: Financial regulators can verify transaction flows without reading private messages
- Reputation system: The reputation system (Course 7) requires transparent transactions to verify that ratings come from real economic activity
- Simplicity: Full metadata protection adds enormous complexity and cost
💡 The Privacy Spectrum
Privacy exists on a spectrum, not as a binary. At one end: everything is public (Bitcoin). At the other: everything is hidden (Monero). Kenostod sits in the middle: financial flows are transparent (enabling compliance and reputation), but communication content is private (protecting business secrets and personal information). This balanced approach serves the majority of legitimate use cases while remaining regulatory-friendly.
Privacy Technologies & Zero-Knowledge Proofs
While Kenostod's encrypted messages protect message content, the broader blockchain privacy landscape includes technologies that can protect not just message contents but also transaction amounts, sender/receiver identities, and communication patterns.
Zero-Knowledge Proofs — A Deep Dive
A zero-knowledge proof (ZKP) allows one party (the prover) to prove to another party (the verifier) that a statement is true without revealing any information beyond the validity of the statement itself. ZKPs are perhaps the most revolutionary cryptographic tool since public-key encryption.
The Ali Baba Cave Analogy
Imagine a cave shaped like a ring with a locked door in the middle. Peggy (prover) claims she knows the secret word to open the door. Victor (verifier) wants proof without learning the word:
- Victor waits outside. Peggy enters the cave and randomly takes path A or B.
- Victor enters and shouts which path he wants Peggy to emerge from (A or B).
- If Peggy knows the secret, she can always exit from the requested path (going through the door if needed).
- After 20 rounds, if Peggy emerges correctly every time, Victor is 99.9999% certain she knows the secret — but he learned nothing about the secret word itself.
Types of Zero-Knowledge Proofs
| Type | Full Name | Proof Size | Setup | Used By |
|---|---|---|---|---|
| zk-SNARK | Succinct Non-Interactive Argument of Knowledge | ~200 bytes | Trusted setup required | Zcash, Tornado Cash |
| zk-STARK | Scalable Transparent Argument of Knowledge | ~50 KB | No trusted setup | StarkNet, StarkEx |
| Bulletproofs | Short non-interactive ZKPs | ~700 bytes | No trusted setup | Monero, Mimblewimble |
| PLONK | Permutations over Lagrange-bases | ~400 bytes | Universal setup | zkSync, Aztec |
ZKPs for Private Messaging
Zero-knowledge proofs open fascinating possibilities for private messaging on public blockchains:
- Prove you sent a message without revealing the content: "I certify that a message was delivered to address 0xABC at time T" without revealing what was said
- Prove message properties without revealing the message: "The invoice amount is between $1,000 and $10,000" without revealing the exact amount
- Anonymous group membership: "I am a member of the authorized senders list" without revealing which member
- Selective disclosure: Reveal specific fields of a message to specific verifiers while keeping the rest private
Privacy Coins and Their Messaging Features
Some blockchains are designed with privacy as a core feature. Understanding them helps contextualize Kenostod's approach:
Monero (XMR)
Uses three key technologies working in concert: Ring Signatures (hide the sender among a group of possible senders), Stealth Addresses (one-time addresses for each transaction), and RingCT (hides transaction amounts using Pedersen commitments). On Monero, all transactions are private by default — there's no option for transparent transactions. Monero supports encrypted payment IDs (similar to Kenostod's message field) that allow recipients to identify payments.
Zcash (ZEC)
Uses zk-SNARKs to prove a transaction is valid without revealing any details. You can prove you have enough funds to make a payment without revealing your balance, the payment amount, or the recipient. Zcash supports both transparent (t-addresses) and shielded (z-addresses) transactions, allowing users to choose their privacy level. The "encrypted memo" field in shielded transactions functions similarly to Kenostod messages.
Secret Network
Uses Trusted Execution Environments (TEEs) to process encrypted data inside hardware enclaves. Smart contracts can operate on encrypted inputs and produce encrypted outputs. This enables private smart contracts and encrypted messaging at the application layer, with the hardware providing privacy guarantees.
Confidential Transactions
Confidential Transactions (CT), proposed by Adam Back and implemented by Greg Maxwell, use Pedersen commitments to hide transaction amounts while still allowing the network to verify that no coins were created or destroyed. The math ensures that inputs equal outputs without revealing what those values are.
✓ Kenostod's Privacy Model
Kenostod takes a balanced approach: transactions are transparent (amounts and addresses are public), but message contents can be encrypted. This balances the need for network transparency and auditability with the need for private communication. The reputation system (Course 7) also benefits from transparent transactions — you can verify that ratings come from real economic activity.
Practical Encryption Workflows
Understanding encryption theory is essential, but applying it to real-world business scenarios is what makes the knowledge valuable. This section covers practical workflows for using Kenostod's encrypted messaging system.
Workflow 1: Freelancer Invoice Payment
A freelancer completes a web development project and needs to receive payment with a proper invoice reference:
Workflow 2: Multi-Sig Approval with Commentary
A DAO treasury requires 3-of-5 signers to approve large expenditures. Each signer can attach an encrypted message explaining their vote:
Workflow 3: Supply Chain Provenance
Tracking goods through a supply chain with verifiable, timestamped messages at each stage:
Workflow 4: Regulatory Compliance Reporting
Using hashed references to link on-chain transactions to off-chain regulatory filings:
- Step 1: Prepare compliance report (SAR, CTR, or other regulatory filing)
- Step 2: Hash the report document: SHA-256(report.pdf)
- Step 3: Send a nominal transaction (0.01 KENO) with plaintext message containing the hash
- Step 4: The on-chain hash proves the report existed at a specific time
- Step 5: If the report is later disputed, the original can be verified against the on-chain hash
Encryption Best Practices Checklist
✓ Encrypt messages containing personal or financial details
✓ Verify recipient addresses before sending sensitive encrypted messages
✓ Keep your private key secure (it's also your decryption key)
✓ Use hashed references for large documents (hash on-chain, full document off-chain)
✓ Include structured data (JSON) for machine-readable messages
✓ Back up your wallet — if you lose your keys, you lose access to all encrypted messages sent to you
✗ Send sensitive information in plaintext messages (visible to everyone forever)
✗ Assume encrypted content hides the fact that communication occurred (metadata is public)
✗ Include private keys, seed phrases, or passwords in any transaction message
✗ Rely on message encryption alone for regulatory compliance (consult legal counsel)
✗ Send encrypted messages to the wrong address (they can never be recalled)
Real-World Case Studies
These real events demonstrate why encrypted, verifiable communication matters. Each case illustrates different aspects of the encryption landscape that Kenostod's messaging system addresses.
📄 Case Study 1: The Sony Pictures Hack (2014)
What happened: North Korean hackers (Guardians of Peace) breached Sony Pictures, stealing and publishing 100 terabytes of data including unreleased films, private emails between executives, salary data, and Social Security numbers of 47,000 employees.
The communication failure: Internal emails discussing sensitive business decisions, personal opinions about celebrities, and confidential negotiations were sent as plain text through corporate email. None were encrypted. The resulting public exposure of executive emails caused massive reputational damage beyond the financial losses.
The lesson for Kenostod users: If Sony's internal communications had used end-to-end encryption, the stolen data would have been useless ciphertext. With blockchain-based signed and encrypted messaging, even a server breach reveals nothing about message contents. The key insight: always encrypt sensitive business communication, even within your own organization.
📱 Case Study 2: WhatsApp's E2EE Rollout (2016)
What happened: WhatsApp enabled end-to-end encryption for all 1+ billion users, implementing the Signal Protocol. This meant that WhatsApp itself could no longer read user messages, even if compelled by law enforcement.
The impact: Governments worldwide protested. Brazil temporarily blocked WhatsApp multiple times. The UK, Australia, and US pushed for "backdoors." However, security experts uniformly warned that any backdoor for law enforcement would inevitably be exploited by criminals and hostile nations.
The lesson for Kenostod users: E2EE is either secure for everyone or secure for no one. There is no mathematical way to create a "golden key" that only good actors can use. This same principle applies to Kenostod's message encryption — the encryption is unconditional. This is a feature, not a bug: weakened encryption protects nobody.
⛓️ Case Study 3: The Silk Road Bitcoin Trail (2013-2015)
What happened: The Silk Road, an online darknet marketplace, was shut down by the FBI in 2013. Despite using Bitcoin for transactions, law enforcement traced Bitcoin transactions through blockchain analysis, identifying Ross Ulbricht as the operator. Over $1 billion in Bitcoin was eventually seized.
The communication angle: While Silk Road used PGP for messages between buyers and sellers, the Bitcoin transactions themselves were fully transparent on the blockchain. Chainalysis and other firms traced the flow of funds, eventually connecting pseudonymous addresses to real identities through exchange KYC records.
The lesson for Kenostod users: Encrypting message content is not enough if transaction metadata (who paid whom, how much, when) is public. This illustrates why understanding the difference between content privacy and metadata privacy is critical. Kenostod encrypts message content but transaction metadata remains transparent — know what is and isn't protected.
🔒 Case Study 4: Lavabit Shutdown (2013)
What happened: Lavabit, an encrypted email service reportedly used by Edward Snowden, was ordered by the U.S. government to hand over its SSL encryption keys, which would have allowed surveillance of all 410,000 users. Rather than comply, founder Ladar Levison shut down the entire service.
The lesson for Kenostod users: Centralized services are vulnerable to government pressure. Even with encryption, a centralized provider holds keys that can be demanded. Blockchain-based messaging eliminates this single point of failure — there's no company to subpoena, no server to seize, no master key to demand. Each user holds their own keys, and the blockchain is distributed across thousands of nodes. This is the fundamental advantage of decentralized encrypted communication.
💰 Case Study 5: The DAO Hack Communication Chaos (2016)
What happened: The DAO (Decentralized Autonomous Organization) on Ethereum lost $60 million worth of ETH due to a reentrancy vulnerability. In the chaotic aftermath, the Ethereum community debated whether to hard fork to recover the funds. Communication happened across dozens of platforms — Reddit, Twitter, Slack, forums — with no verifiable attribution or timestamps.
The communication failure: Fake "insider" posts influenced market panic. There was no way to verify who actually voted for or against the fork. Community members impersonated core developers. The lack of signed, verifiable communication channels contributed to confusion and market manipulation.
The lesson for Kenostod users: If DAO governance communications were cryptographically signed and tied to on-chain identity (as Kenostod messages are), impersonation would be impossible. Every governance communication would be verifiable, timestamped, and attributable. This is exactly the use case Kenostod's message signing was designed for.
Written Exercises
Complete these exercises to reinforce your understanding. Take your time — thoughtful answers demonstrate true comprehension.
Exercise 1: Explain Encryption to a Friend
Your non-technical friend asks: "What's the difference between symmetric and asymmetric encryption?" Explain both using real-world analogies (no technical jargon). Include why we need both types and how they work together in a hybrid system.
Exercise 2: Privacy Analysis
A company wants to use Kenostod for payroll. They want to include salary details in transaction messages. What privacy considerations should they think about? Consider both the message content AND the transaction metadata. What would you recommend regarding encryption vs. plaintext messages, and why?
Exercise 3: Comparing Messaging Systems
Compare Kenostod's on-chain encrypted messaging with Signal messaging and PGP-encrypted email. For each, describe: (1) who can read the messages, (2) how long messages persist, (3) what metadata is exposed, and (4) what legal evidence value they have. When would you choose each system?
Exercise 4: Case Study Analysis
Choose one of the case studies above (Sony, WhatsApp, Silk Road, Lavabit, or The DAO). If that organization had used Kenostod's encrypted transaction messages instead of their actual communication method, how would the outcome have been different? Analyze both what would improve AND what limitations would remain.
Exercise 5: Design a Messaging Use Case
Design a real-world business scenario where Kenostod's encrypted transaction messages would be superior to any existing communication method. Describe: the scenario, what information would be in the message, whether it should be encrypted or plaintext, what metadata considerations exist, and why blockchain-based messaging is the best fit.
Hands-On Lab
Now it's time to put your knowledge into action! Complete ALL of the following tasks in the Kenostod blockchain simulator.
Lab Tasks:
- Task 1: Send a Plain Message — Go to the Send KENO tab and send a transaction with a plaintext message attached. Observe how the message appears in the transaction record.
- Task 2: Send an Encrypted Message — Send another transaction, this time with encryption enabled. Notice how the message appears as ciphertext in the blockchain explorer.
- Task 3: Verify a Signature — Receive a transaction with a message and verify the cryptographic signature. Confirm that the message was indeed sent by the claimed sender.
- Task 4: Decrypt a Received Message — Open a transaction you received that contains an encrypted message. Use your private key to decrypt and read the contents.
- Task 5: Explore the Blockchain — Browse transactions in the Blockchain Explorer. Compare how plaintext messages vs encrypted messages appear. Note the metadata that's visible even for encrypted messages.
Opens in the main platform. Complete all 5 tasks, then return here for the Final Exam!
Final Exam (12 Questions)
You must score at least 10 out of 12 correct (80%) to complete this course and earn your 250 KENO reward. Take your time and review the material if needed.
1. What makes Kenostod transaction messages different from regular email?
2. Who can decrypt an encrypted Kenostod transaction message?
3. What was the significance of the Diffie-Hellman key exchange (1976)?
4. What is the main advantage of symmetric encryption over asymmetric?
5. What is ECIES and why does Kenostod use it?
6. What is the difference between transport encryption and end-to-end encryption?
7. What three guarantees does a digital signature provide?
8. What is a zero-knowledge proof?
9. Why is metadata still a privacy concern even when message content is encrypted?
10. What key feature does the Signal Protocol provide that Kenostod messages do NOT?
11. What is Kerckhoffs's principle?
12. Why is on-chain messaging valuable for business despite being more expensive than off-chain alternatives?
Kenostod Blockchain Academy © 2024-2026
← Course 5 | Home | Course 7 →